In 2022, Shenzhen Cyber Security Propaganda Week "Rule of Law Day" is here!Prevent "risk on your fingertips", have you get these knowledge points?
Author:China Youth Network Time:2022.09.09
Cyber security is the people, and network security depends on the people. Shenzhen Cyber Security Propaganda Week "Rule of Law Day" is here!
Holding the Weekly Cyber Security Publicity Week and improving the awareness and skills of the national network security is an important part of national network security work. Since 2014, the state has held eight -time cyber security propaganda week.
Recently, the Shenzhen Municipal Public Security Bureau took the lead in organizing the "Rule of Law Day" theme publicity activities of Shenzhen Cyber Security Propaganda Week in 2022. Through online and offline linkages, the public security branch and relevant police species of various districts and relevant police species were carried out. Essence The Municipal Public Security Bureau gives full play to the advantages of Shenzhen Public Security New Media Matrix, and released the mainstream network platforms such as Sina Weibo, WeChat public account, Douyin, and today's headlines to release network security prevention promotional posts and video short videos. The business center plays the network security weekly promotional video; the traffic police department carries out the "network security accompanied by our travel" activity, using the city's traffic display, rolling the network security weekly promotional gold sentence ... The upsurge creates a good atmosphere of learning the knowledge of network security together.

Just as the Internet Security Propaganda Week, Shenzhen Police will send a security tip to you on the "surfing expert" online to help you prevent the "risk on your fingertips".
01 Prevent telecommunications network fraud
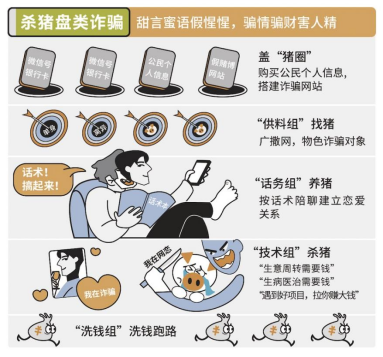
Emotional investment fraud. In the name of dating, through the cultivation of emotional acquisition trust, and then tempting the victims to fund and invest, thereby implementing the fraudulent technique of collecting money, commonly known as "killing pig plates". "Killing a piglet" is usually a gang crime. The criminals set up a "gentle" trap. Caring for the victims is false and fraudulent money is true.
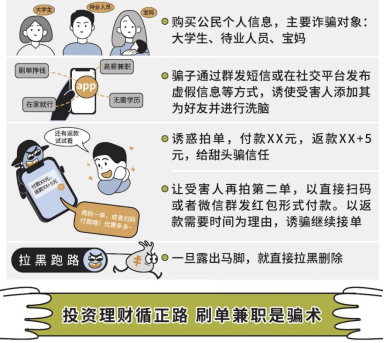
Swipe orders, part -time fraud. It is said that scammers attract victims by publishing high -paying part -time information, and then continue to encourage the victims to invest money through the routine, and eventually deceive all cheats of investing money, commonly known as "killing birds".
Prevent telecommunications network fraud, please keep in mind the following protection suggestions:
The first is to protect personal information. No important information such as identity card numbers and family addresses to strangers. The second is to make friends with caution. When making friends online, pay attention to the identity of the other party, and do not trust strangers casually. The third is not to disclose the password. Set a password with a high degree of complexity for bank cards, online banking, and mobile banking, and do not disclose or forward the SMS verification code or other forms of dynamic passwords to anyone. The fourth is to run business through official channels. To handle the business and other businesses, you must apply through reliable channels such as banking Fang WeChat and official websites. Do not trust strange numbers SMS or call. Fifth, don't click the link easily. Most of the links in the SMS are fishing websites. Once you click the link to enter the website, the personal information you fill in will be obtained by the scammer in the background of the website.
02 Preventing network security threat
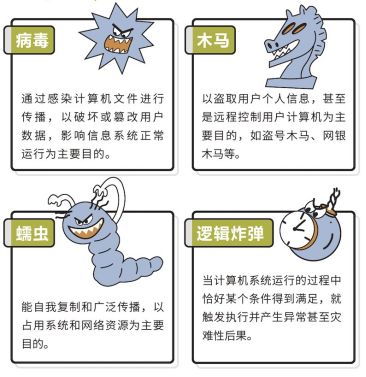
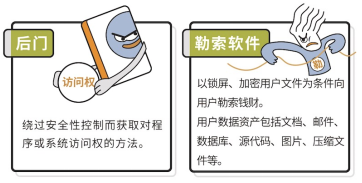
If your device has a typical situation such as often crashing, data loss, a large number of unknown documents, and automatic execution of operating systems, it is likely that it is an attack on malicious software such as viruses and Trojan, and immediately check the virus!
Stay away from network security threats and focus on preventing skills!
ü To install firewalls and anti -virus software, and update the virus feature library in time
正 To download the genuine software from the official market, patch the operating system and other software in time
ü To set a password for the computer system account, delete or disable the expired account in time
ü Use anti -virus software to check before opening any mobile memory
ü The systems and data of the computer and mobile phone should be backups regularly, pay attention to the abnormal warning, and repairs the restoration in time to click "X" to close the pop -up window
Intersection Don't open the short link in the webpage, mailbox link or text message in unknown origin
Intersection Do not execute download software without anti -virus software
Intersection Don’t open the unknown file received on the QQ and other chat tools
Intersection Don't trust the pop -up information of the webpage
Intersection Don't click on any non -expected dialog box
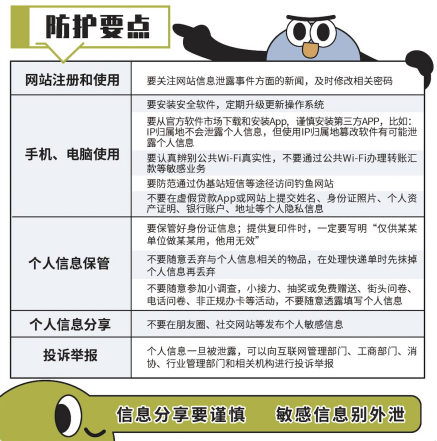
03 Preventing personal information leakage
Generally speaking, there are three ways to leak personal information. The first is to be sold by some unscrupulous companies and institutional employees. The second is because downloading the unknown APP, the public Wi-Fi randomly, the use of unknown charging treasures, and clicking on the website link, etc., causing the information to leak from the mobile phone. Third, hackers use website vulnerabilities to implement invasion and steal the database of saving information, commonly known as "drag library".

For the general public, please protect personal information carefully when surfing the Internet.
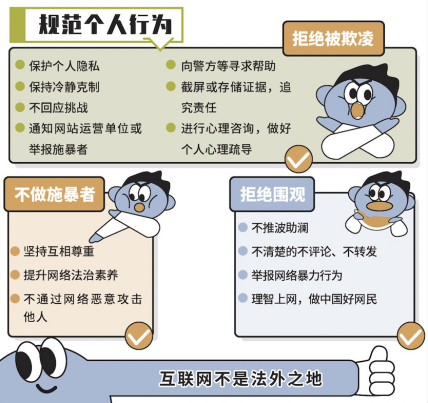
04 Prevention and control network violence
Network violence is an Internet users publishing words, pictures, videos and other behaviors such as harmfulness, insults, and incarnation on the Internet, and cause damage to the reputation, rights, spirit, and privacy of others.
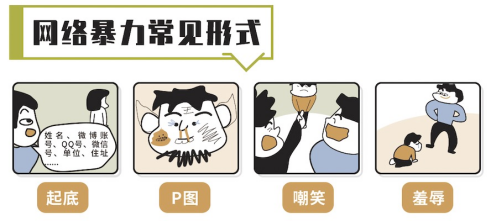
Perigues in cyber violence often take the name "moral justice", and continue to attract attention through labeling and emotional venting; while victims often face the problems of difficulty obtaining evidence and defending rights, and have to choose tolerance and silence.
However, the Internet is not illegal!
Article 1,194 of the Civil Code: Those who use the Internet to infringe their civil rights and interests by using the Internet to infringe on others.
Article 1,195 of the Civil Code: If the Internet users use network services to implement infringement, the right holder has the right to notify the network service providers to take necessary measures such as deletion, shielding, and disconnecting links. The notification should include preliminary evidence that constitutes infringement and the true identity information of the right holder.
If the circumstances are harsh and the social order destroys the social order, it can also be held criminally responsible in accordance with Article 293 of the Criminal Law.Today, the Internet has integrated into all aspects of social life, and has profoundly changed people's production and lifestyle.Work, severely crack down on network crimes, and make every effort to protect the security of the network space.
In 2022, Shenzhen Cyber Security Publicity Week, let us learn network security knowledge together, build network security together, and share network civilization!(Sun Dandan)
- END -
Yanji Municipal CPPCC conducts a special survey of optimizing business environment

On July 15, members of the Federation of Industry and Commerce of the Yanji Munici...
Father's Day dedication to caring for the old man
On June 19, the 77 -year -old Zhong Chuanxing, who lived in Xindu District, Chengd...