Be careful of "drinking tea"!U.S. Attacking Western University of Technology's technical details exposure
Author:China Daily Time:2022.09.13
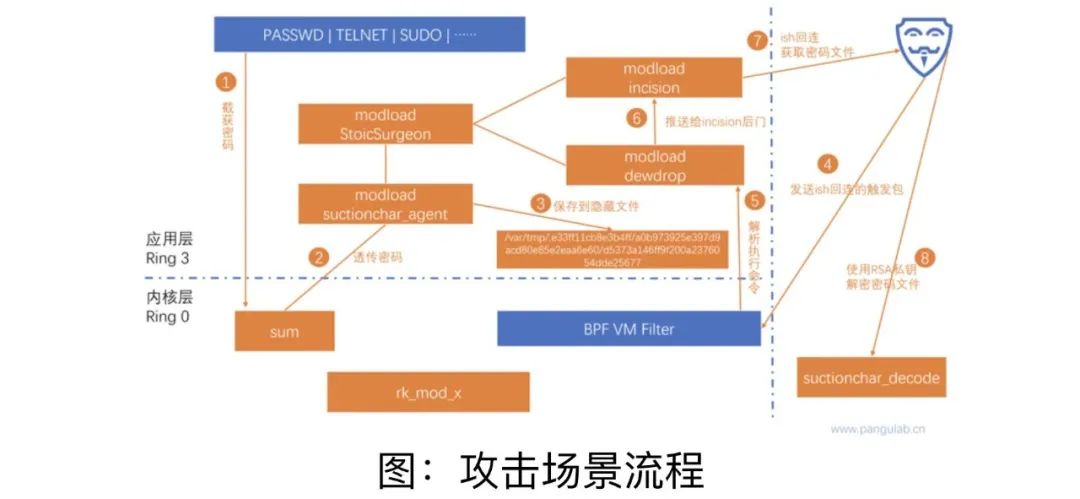
On September 5, relevant Chinese departments announced to the outside world that Northwest University of Technology had previously stated that it was attacked by overseas network attacks. The attacker was the National Security Agency (NSA) specific invasion action office (TAO). Since then, the National Computer Virus Emergency Treatment Center and Beijing Qi'an Pan Gu Lab have further analyzed the invasion. In the latest survey report, the technical details of the US implementation of attacks were made public: that is, the 41 network weapons were named "Drinking Drink "Tea" Sniches's Secret Secret Network weapons are one of the most direct "culprits" that lead to a large amount of sensitive data.
According to the relevant network security experts, TAO uses "tea drinking" as a sniffing tool, implanted it into the internal network server of Northwestern Polytechnical University, stealing the login password of remote management and remote file transmission services such as SSH The access permissions of the server realize the horizontal movement of the intranet, and send other high -value server to other high -value server to send other sniff, persistent control, and hidden disappearance network weapons, causing large -scale, persistent sensitive data theft.
According to technical analysis and research, "tea drinking" can not only steal the account password of a variety of remote management and remote file transmission services on the server, but also have strong hiddenness and environmental adaptability. The network security experts in the above said that after the "tea drinking" is implanted into the target server and network equipment, it will disguise itself into a normal background service process, and use a modular method to send malicious loads in stages. Hiddenness, it is difficult to find. "Tea Drinking" can be operated hidden on the server, monitor the user's input on the terminal program of the operating system console in real time, and intercepts various user names and passwords, like the "voyer" standing behind the user. Cyber security experts introduced: "Once these username passwords are obtained by TAO, they can be used to attack the next stage. Even if these usernames password access to other servers and network devices, they will steal files on the server or send other delivery of other. Network weapon. "

National Security Agency (NSA) Headquarters, Mideburg, Maryland
Technical analysis shows that "tea drinking" can effectively integrate and link with other NSA network weapons to achieve "seamless docking". In February of this year, the Beijing Qi'an Pan Ancient Laboratory publicly disclosed the technical analysis of the top weapon "Electric Screen Operation" (BVP47), which is affiliated to the National Security Agency (NSA) hacker organization- Anpan ancient named "Electric Screen Action" attack activity. In TAO's incident of cyber attacks on Northwestern Polytechnical University, the "Tea Drinking" sniffing theft tools and BVP47 Trojan Programs were cooperated with other components to implement joint attacks. According to the introduction, the BVP47 Trojan has extremely high technical complexity, architecture flexibility, and ultra -high -intensity analysis and evidence collection and confrontation characteristics. It is used to peep and control the information network of the victims with the "tea drinking" component, secretly stealing important data. Among them, "Tea Drinking" sniff the hippocampus secretly lurking in the information system of the victims, and is responsible for listening, recording, and returning the "results of the war" -the account number and password used by the victims, whether it is in the inner network or the external network Essence
The report also pointed out that with the gradual deepening of the survey, the technical team also found the "tea drinking" attack traces in other institutions outside Northwestern Polytechnical University. Network attack activities.
It is worth noting that in the multiple cyber attack activities implemented by the United States, the US IT industry giants have repeatedly appeared. For example, in the "Prism" plan, the US love department has the authority of senior administrators and can enter the servers of Microsoft, Yahoo, Google, Apple and other companies at any time, and the long -term secrets are tailored. In the hacking tools used by the "Formula" organization announced by the "Shadow Broker", Microsoft, Cisco, and even some Chinese Internet service providers' "zero vulnerabilities" (0Day) or back doors appeared. "The United States is using its technical dominance in the field of software and hardware in the network information system. With the comprehensive cooperation of the US IT industry giant, using a variety of cutting -edge network weapons to launch non -different network attacks worldwide in global The account password is prepared to log in to the victim's information system at any time to implement a larger scale stealing or even destroying activities. Its network hegemony is undoubted. "Therefore, network security experts suggest that users, especially network operations, and maintenance of network operations and maintenance. The server is reinforced, the administrator passwords of the server and network devices are regularly changed, and the audit of the network network traffic is strengthened, and the abnormal remote access request is found in time. At the same time, in the process of informatization, it is recommended to use domestic products and "zero trust" security solutions. ("Zero trust" is a new generation of network security protection concepts. No one, equipment, and systems inside and outside the network default.)
This expert further pointed out that whether it is data stealing or system destruction and paralysis, network attack behavior will cause huge damage to network space and even the real world, especially for attack behavior for important key information infrastructure. The mapping, the characteristics of network activities easily across the border, make it a pioneer of continuous struggle. Without network security, there is no national security. Only by developing our asymmetric competition in the field of science and technology can we establish a China, independent and independent network that belongs to China, independent and independent networks. Protection and confrontation ability. "Source: Global Times-Global Network

- END -
"Weilong", "Kunpeng", "Auspicious Bird" ... the aircraft industry releases aircraft product brand naming rules
The picture shows the J-20 Weilong (Photo Conferring of China Aviation Industry Gr...
What ways do you want to be a "soldier teacher"?Interpretation is here →

Picture source network.On June 20, the city issued the Xiamen City to Implement th...